As a counter-argument to my previous post as to why you shouldn’t get a smart meter for your electricity and gas, here’s a list of reasons why you perhaps should.
I would suggest though waiting for your supplier (I use Bulb Energy and do recommend them – plus if you switch with my affiliate link we both get £50 credit and cheap gas and electricity) to roll out ‘SMETS2’ smart meters as these will continue working ‘in a smart manner’ no matter which supplier you are with whereas ‘SMETS1’ (the ‘current/previous’ generation) ones usually stop reporting meter readings when you switch suppliers or their in-home displays become inaccurate/stop working.
- Reducing running costs. Suppliers no longer need to send out meter readers to get accurate readings (especially from people who can’t/won’t provide readings themselves). This means they can keep their prices low and give you lower bills
- More accurate bills. Provided your meter reading a day or two early or unable to read your meter one month? Then you were probably getting an estimated bill – now with the data flowing to the supplier, you needn’t worry as they supplier can get the meter reading just when it is needed for your bill.
- Accessibility. A lot of people have no problems accessing and reading their meter, but others may have mobility problems, dyscalculia (‘dyslexia with numbers’), or the meter could be in a hard to access place (too low/high or in another building entirely under control of a nearly absent landlord). Smart meters means you don’t have to worry about reading it yourself.
- Detecting problems. Since the meter reports back to the supplier quite frequently, the supplier could notify you (or the local distribution network) if the usage is out-of-standard: left an electrical heater on in your garage for the last couple of days (whistles innocently) – then they could drop you an email saying ‘Check your appliances’. Likewise, elderly and disabled customers could have their power monitored and if it doesn’t have ‘customary peaks’ (i.e. kettle going on, tv usage) for 2 days, alert ‘next of kin/police/social services’ for a check-up.
- Customer education. Smart meters allow customers to easily see what is using their power/gas and adjust their usage in an intelligent manner (instead of just guessing) – we all ‘know’ filling your kettle to just the amount you need saves power, but if you’ve got an in-home display next to the kettle you can test it yourself and reinforce that knowledge.
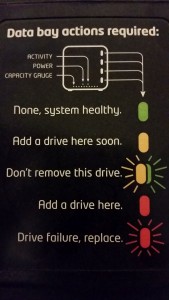
- Flexible tariffs. Instead of having to get a physical meter swap to go between prepay, credit, Economy 7 – this can be remotely set by the supplier. Prefer to use a custom ‘smart meter’ tariff which has multiple rates during the day based on ‘grid demand’, then that can be done – allowing you to have cheaper power at lower demand times.
- Grid protection. Usually only applicable for heavy users (factories and the like) – under times of ‘unusually high demand’ (winter peak times for example), the supplier/national grid could then turn off the meters remotely to protect the National Grid from overdemand. This isn’t a new thing (the companies already have ‘shutoff’ agreements with heavy users), but it’s usually a manual process where they company is called and asked to cease operations. With smart meters, they can be provided with an ‘At risk’ notification (as they tend to do in the mornings now I believe) and if it comes to it, NG can shut things down and restart things just for the minimum time necessary.
- Environmental. I believe it’s easier to integrate ‘feed in’ items such as home solar panels and the like to smart meters rather than having to have multiple meters for it.
- Better home control. With smart meters supporting Zigbee (the same protocol used by ‘smart lights’), it is possible customers can have their in home systems integrate with it automatically – no need to bother manually adjusting storage radiators or timer switches on washing machines – with an integrated smart home, everything can come on at the cheapest time for you.
- Better flexibility for generators. At the moment, most Economy 7 and the like meters in a region are roughly the same time – but those times tended to be based on 60s-80s electrical usage patterns: but we don’t have many coal mines, steel factories, and other heavy usage factories nowadays – and in some areas, most people work 9-5 jobs meaning ‘peak times’ are now 9-5 instead of the traditional 6-2pm for factories. Smart meters will allow these times to be adjusted in smaller regions (or even nationwide) as the grid supply/demand curve changes: ensuring we don’t need too many generators ‘available’ at a time which then go idle 75% of the time.
On the flip side, have a look at my list of reasons why you perhaps shouldn’t get a smart meter.
No matter who you get your gas/electricity from, you do want it to be cheap and environmentally friendly – perhaps consider switching to Bulb Energy. I’ve been with them since December 2017 and am more than happy with them (in fact, the majority of this post has been copied from a post I originally wrote on their community forums), and if you switch using my affiliate link here, we’ll both be credited with £50 and you’ll get 100% renewable electricity, 10%+ green gas and lower costs than the ‘big six’ and most of the other suppliers.